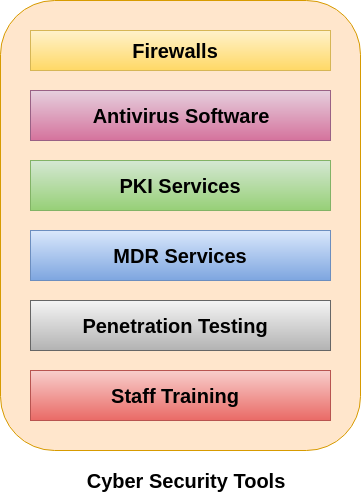
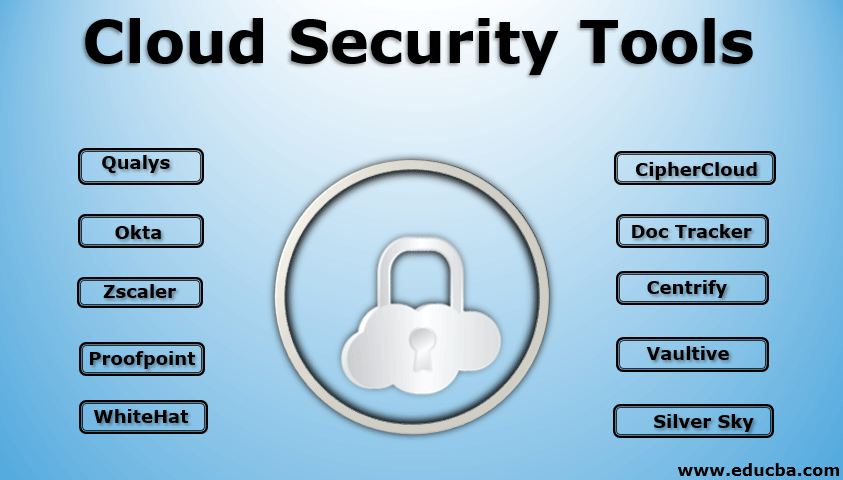
Chapter 75: Cyber Security Assessment Tools and Techniques | A Book: Nuclear Energy – Peaceful Ways to Serve Humanity.
ICT Security Tools and Techniques among Higher Education Institutions: A Critical Review | International Journal of Emerging Technologies in Learning (iJET)